I spent only a couple of hours today working with Claude Sonnet 4.6 on a long-planned feature for this application. It's not exactly a blog feature, and in fact initially it will only show up in the Calendar. I'm just psyched because in a short time working with Claude, I got a full spec for the feature, which Claude then used to create a passable first draft of it. A couple rounds of tweaking both the spec and the code later and I sent it to the dev/test environment.
I'm still not 100% on board with building the spec to perfection and only then having the model build the code. Iterating helps me really understand what the software does, especially when it includes UI elements. So why have Claude write a spec? Because tomorrow, when I resume work on this feature, Claude can simply read the spec to understand everything we've done today, which saves tens of thousands of tokens and keeps us walking down the same path. Vibe coding, by contrast, would require that Claude reverse-engineer the feature it just build in order to understand where to go next.
The dogs are both pestering me, however, so it's time to go outside.
Pinned posts
- About this Blog (v5.0) (2 months)
- Brews and Choos project (3 weeks)
- Chicago sunrises, 2026 (4 months)
- Inner Drive Technology's computer history (2 years)
- Logical fallacies (6 years)
- Other people's writing (5 years)
- Parker Braverman, 2006-2020 (5 years)
- Style sheet (10 months)
- Where I get my corn-pone (3 months)
I plan to spend a lot of time outside with the girls today, because it looks like this:

Butters has found a sunbeam and may not want to move right away:

She's so cute, one could almost forgive the puddle of urine she presented to me in my bedroom yesterday morning. Or how she refuses to walk more than 3 km at a stretch, unless she gets a lot of time to rest, while Cassie and I just wait for her. In fairness, she has short legs and she might have arthritis. I think she may be older than initially assumed, closer to 10 than to 7, which adds to the arthritis hypothesis. Of course, the beagle theory would operate in any event. I'm glad Garmin's monthly 5 km walk challenge is next weekend, I have to say.
I just read the transcript from Thursday's hearing before US District Judge April Perry, in which acting US Attorney Andrew Boutros dismissed charges against the defendants with prejudice after admitting his office committed prosecutorial misconduct in the grand jury proceedings against the six last October.
It's an interesting read, whether or not you understand the legal nuances. District court judges have been the ones holding the OAFPOTUS's droogs to account. I'm glad to see it happening, and I hope it continues. Of course, the US Supreme Court keeps letting them off the hook, but we'll deal with that soon enough.
Putin loses another ally
Director of National Intelligence Tulsi Gabbard will resign according to what I can only imagine to be gleeful "sources in the intelligence community," officially because of her husband's cancer diagnosis. Her ties to Russia have been well-known for years. Russian dictator Vladimir Putin must be furious.
Meanwhile:
- The OAFPOTUS's "Deserving Fascist Slush Fund" hit a snag last night as Republican Congressional leaders buggered off for the holiday rather than vote on it.
- The slush fund, which could well be DOA given how many Republican senators the OAFPOTUS pissed off this week, is the most corrupt proposal in US history, which shouldn't surprise anyone but is nonetheless shocking.
- Radley Balko takes us through the shooting of Julio Cesar Sosa-Celis and the brazen lies that Immigration and Customs Enforcement have told about the case.
- Prosecutors in Chicago committed actual misconduct according to the judge overseeing the "Broadview Six" case, so she dismissed the entire thing with prejudice.
The upshot may be, as James Fallows suggests, that we have turned a corner on the OAFPOTUS. That won't make the Republican Party any less corrupt or authoritarian as a whole, but we may finally be seeing Republicans in Congress fed up with the insanity. The insanity they supported until now, I should note.
OK, back to work I go, hoping against history that my own party's leadership can get their heads out of each other's asses long enough to win back Congress in five months. With the New York Times, Quinnipac University, and AltasIntel all having us above +10% on the generic ballot, at least we'll have numbers if not an actual strategy.
Once again, I'd like to point out that I have one of the best views in Chicago:

That's Wednesday around 6pm. Even though my apartment faces east, the sunsets are amazing.
Also, Butters may have her annoyances, but she's kind of cute, whether engineering a comfy sleeping fort:

As a Butters Burrito to calm her down after someone lit off a firecracker that no one but she heard:

Or giving side-eye while snoring a few minutes ago:

She's about to get a 3-kilometer walk around Montrose Harbor today, and very likely a 6-kilometer round-trip to Begyle/Dovetail Mayfestiversary tomorrow.
I'll whinge about politics later this afternoon, especially about the most corrupt proposal ever made by a sitting US president.
I had a bunch of errands to run today, including a trip down to City Hall to change my city car registration. (Yes, you have to do that in person if you're getting a parking zone added.) However, long experience with Butters tells me I can't really leave her alone for more than a few minutes. "Alone" in this case means "without human supervision," as even with Cassie present, Butters does a passable impression of an air-raid siren if she discovers she is without human company. I assume that keeping her for months or years would help her understand that the world won't end if she's alone for an hour, simply because after a couple of years she stopped baying when her own humans left her alone in their house.
In any event, I managed to turn today into a couple of bonus walks by taking Butters to day camp by car, returning home, and walking Cassie to the same place. Cassie, of course, looked bewildered when I left with Butters and not her, but she didn't start bellowing as Butters would have done had the roles reversed. Then Cassie and I got to day camp in 19 minutes at an average pace of 8'44" per kilometer. Contrast this with yesterday's walk of about the same distance with Butters, which took over half an hour at an average pace of 11'28" per kilometer.
I've got one more errand to run before reversing the process: Divvying over to day camp, walking Cassie home, then driving back to day camp to fetch Butters.
I hope the weather is warm enough this weekend that I can take them both someplace social. It might get up to 20°C Sunday and 19°C Monday! Who knows? We might even make it all the way to Begyle (2.8 km) for their Mayfestiversary party. I know Butters can walk that far because she managed it yesterday; but will she tolerate the crowds? With the amount of barbecue people drop at the event, I suspect so. Stay tuned.
It took me 3 hours to fix a bug in the way Weather Now finds weather lists for logged-in users. Simply put, the app could read private weather lists except when trying to edit them, which was kind of annoying. Even Claude had some trouble figuring this one out.
Unfortunately, I had rather hoped to fix a big performance problem with this app, but at least I started writing the spec on that. And I walked the dogs for over an hour. And started setting up the laptop that I finally got to replace my 11-year-old Surface Pro. I went with Framework and got a DIY model that was really very simple to D.
And now, the dogs get another walk. It's an unseasonably cold 13°C with pretty stiff winds (26 km/h gusting to 43 km/h). They're wearing fur coats; I'll need to dress for early April.
What does Xi know that you don't?
Let's start our round-up of the day's news with a note from Francis Fukuyama, leading with "It was both painful and humiliating to watch media coverage of Donald Trump’s recent visit to Beijing" and getting more depressing from there. Yes, and:
- The OAFPOTUS and the Justice Department that he controls "agreed" never to investigate the obvious tax improprieties the entire Trump family perpetrates now and "in perpetuity," or at least until someone enforces 26 USC 7217, the "prohibition on executive branch influence over taxpayer audits and other investigations." Or until half a million citizens file actions under the False Claims Act.
- Josh Marshall calls this and other obviously corrupt acts "a kind of bust-out phase, realizing that his power is ebbing and you need to grab every dollar on the table, cross every line while it’s still possible."
- Paul Krugman says MAGA corruption has reached the point of no return as the OAFPOTUS loots the country. "I would argue that the blatant nature of the new looting is a signpost of where America under Trumpism is heading in the months and years ahead. So you can think of the $1.8 billion slush fund as a promise to MAGA-world that there is a payoff to be had if they just stick with him for the next two and a half years." Dan Rather agrees.
- Brian Beutler predicts that Illinois governor JB Pritzker will win the Democratic primary in 2028, and wow do I hope so. Or maybe Georgia's junior US Senator, Jon Ossoff? That works for me too.
- Speaking of corruption (do I do anything else?) and closer to home, Chicago Parking Meters LLC appears to have been sold to a private-equity group in New York. The Chicago City Council still has to approve the measure, and the only mayor we have backed us out of a deal for the city to buy the revenue back. That's OK, the deal only has another 50 or so years to run.
Finally, Jeff Maurer rages against what postal mail has become, and I can't disagree after trying to get my Real ID renewed last week. My recurring joke, which is more an expression of sadness than humor, is that the Post Office has delivered my recycling again. "Not only am I paying for trees to be cut down, sent to my house in the form of chores, and then hauled away again, but I’ll also get in trouble if I miss the oh-so-important needles that are mixed into the haystack. I am enrolled against my will in a system that feels like some shit The Riddler dreamed up," he writes. He's not wrong.
I've closed three big Jira cards on Weather Now in the last three days, two of them new features. The bug fix was a pretty straightforward vibe coding, using Claude Sonata 4.6 iteratively to fix a bug. Basically, that means I had a conversation with it, watched it make changes to the code, then I tested the code and gave it feedback.
The new features (which are closely related) were more deliberate. Claude actually made the changes to the code, with just a little polishing afterward from me. But the conversation was about the specification, not the code itself. Instead of starting the session with "Here is a bug, let's fix it," I started with "Here is the beginning of a spec, let's write it in a way that you can use to write the code."
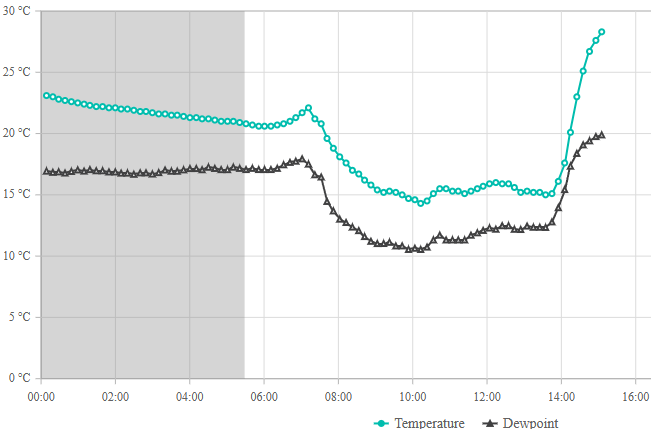
The new feature, by the way, allows you to compare two weather stations to each other for the past day. For example, here is the comparison between O'Hare and Lakeview/Pine Grove. The Lakeview station is only 580 meters from Lake Michigan, while O'Hare's weather station is 21.3 km from the nearest shoreline. So this comparison is particularly useful on days with strong lake cooling, like last Sunday. (I wrote about the front passage that afternoon.)
Note that you have to have a free user account to view station history. It keeps the bots away. Google and Microsoft accounts both work.
Unfortunately, there's a minor bug with the feature that I will now attempt to fix by writing a bug report Claude can use to fix it. This is the way of the future.
Despite Butters peeing on my floor due to the terror of living through a thunderstorm this morning, even while Cassie thought nothing of it and probably wondered why Butters was so anxious, Butters is kind of cute. She has a propensity to engineer sleeping spaces, for example. On Saturday, no one could possibly find her:

She also tends to sleep with her eyes open, which can be disconcerting and leads to the belief that she exists in a constant state of giving side-eye:

As for the floor, not to worry; it's manufactured wood, and I have plenty of Nature's Miracle on hand.
Bitunlockedered
Someone has discovered a way to get around Bitlocker encryption, and somehow that wasn't the worst thing I read this morning:
- Have you ever noticed how Republicans wreck the economy every time they have power? Aren't you tired of that?
- Like, for example, how the OAFPOTUS and his droogs have run up the national debt to 100% of GDP?
- This is what happens when people return to believing demons walk among us because nothing says "modern America" like a return to the 14th Century.
- And because of the OAFPOTUS's inability to get through the day without drooling, China really doesn't have to worry about the Thucydides Trap that Chinese premier Xi Jinpeng mentioned during the summit last weekend.
- Of course, my party can't seem to grasp the urgency of fixing democracy before turning to our pet policies, so there's that.
- The Washington Post helpfully provides "seven charts that explain why the job market is so tough right now," in case you were wondering.
Finally, Sam Sianis, who owned the Billy Goat Tavern of "cheezborger" fame, has died at 91. Thanks to the original cast of Saturday Night Live coming almost entirely from Second City,
It was at this subterranean location on Lower Michigan that Mr. Sianis became famous for telling customers in his thick Greek accent: “Cheezborger, cheezborger, cheezborger. Cheeps, no fries, Coke, no Pepsi,” thanks to a 1978 Saturday Night Live skit that mimicked him.
Not to mention, "Mr. Sianis’ uncle, William Sianis, was behind the legendary “Curse of the Billy Goat” that some believed plagued the Cubs for decades."
Now if Butters could only understand that the thunderstorm outside will not actually hurt her, I might get through the next week without washing every towel I own. Even Cassie rolled her eyes.
A stationary front settled over the Chicago area overnight, drifting north through my area around 8am and drifting back south around 2pm. As those overlapped almost perfectly with when I walked the dogs today, I got to be incorrectly dressed twice. When I walked the girls at 8am, the temperature was drifting down from 20°C to 15°C; just now it vaulted from 15°C to 28°C (with a heat index over 30°C):
Both dogs are now splooting on my floor.
Tomorrow, the forecast says a cold front will pass through with rain and thunder, bringing the high to only 12°C on Wednesday. Turns out, both dogs and I enjoy that temperature.
I will now close my windows and hit the A/C.
Warm day, sleeping dogs
Cassie, Butters, and I took a 40-minute walk to the lake and back in a 28°C heat index an hour ago, and both of them are passed out on various surfaces. Good, especially in Butters' case. (As I typed this, Cassie came over to investigate.)
Time for a round-up of my open browser tabs:
- Robert Wright calls the OAFPOTUS's trip to Beijing "an accidental triumph" even while Adam Kinzinger points out the obvious hypocrisy, and why that doesn't matter to MAGA.
- Speaking of hypocrisy, David French looks at the Southern Baptist Convention and the people who drove it far-right.
- Brian Beutler once again screams into the wind about the Democratic Party failing to punish cheating by the other side. "Democrats can’t stop Republicans from testing the limits of their power. In many cases they can’t even be certain that their resistance will be adequate to reversing the injustice. But they can create painful friction."
- Are dating apps dead?
- The last of the Eamus Catuli buildings has been demolished. Sad.
And let's all remember Hannah Arendt's assertion, quoted the other day by Paul Krugman: "Totalitarianism in power invariably replaces all first-rate talents, regardless of their sympathies, with those crackpots and fools whose lack of intelligence and creativity is still the best guarantee of their loyalty." The OAFPOTUS shows why.
Look who's come to visit:

Her people left about 3 minutes before I snapped this photo, which explains her anxiety. This soon gave way to annoyance when Cassie started squeaking a toy right in her ear:

Butters will be here for a few days. Unfortunately, given her abandonment issues and extraordinary lung capacity, I can't leave her alone at all. This means Butters will get a lot of walks with Cassie so I can maintain my step count.
One more photo from today. A warm front pushed through this morning, causing an unusual roll cloud:

We expect thunderstorms tonight, which I hope will give me some cool lightning strikes over the lake, but which I fear will send Butters over the edge. Fortunately her folks left me with some CBD treats. I hope (a) Butters doesn't become her usual hide-under-the-furniture self when the storms hit, and (b) the CBD treats work if she does. Should be an exciting evening! (For the record, Cassie doesn't care much about thunderstorms as long as she's not getting soaked.)
I went to the DMV both yesterday and today because yesterday I didn't have the exact documentation required to update the address on my REAL ID driver's license. Well, ha ha ha, today I also didn't have the exact documentation required. Because it turns out, even though "official mail from a state agency" is one of the acceptable forms, wouldn't you know that if it's from one specific part of the state government, it isn't acceptable? You'd think they would call that out.
So I said fuck it and just got a regular renewal, because I also needed to update my car registration (next building over), and I had already wasted over 2 hours of my life driving to and from the place already.
I'll get the fucking REAL ID when I get my updated license, because (they're so droll!) the updated license counts as proof of residence. Puzzle out that logic.
I think they enjoy this shit.
Today I have to go to the DMV, the bank, and the barber, plus handle a few dozen other small tasks. Cassie will also get plenty of walkies as befits her caninity. This is our weather today:

I'll have some time this afternoon to catch up on the news.
Strangely anti-climactic
I no longer own a house. This state of affairs will continue for quite a while. Since September 1998 I have owned property continuously except for 4 days in 2000 and 3 days in 2018. The flipside of this is that I no longer have a mortgage. No property, no debt; what will that do to my FICO score? I'll have to wait until mid-June to find out.
It doesn't feel like anything happened, though. We no longer sit around a table at the title company and sign documents; the attorneys do it over Zoom, and the principals just go about their business. I miss the old days.
I still love the view from my new place, though. Who knows, I might stay here for longer than I expected.
Meanwhile, out in the rest of the world:
- The pathetic, demented OAFPOTUS posted 55 times on social media within a 3-hour window Monday night, and all of it was gibberish. So why does the Republican Party still insist he's capable of doing his job?
- Nate Silver uses Math!™ to demonstrate how there is no trade-off between Democratic redistricting efforts and electing Black representatives.
- Of course, this only matters if Democrats make sure Republicans face consequences for violating the norms of democracy.
- Paul Krugman calls the attack on Iran "the apotheosis of willful ignorance."
- No, you absolute apes, Israel did not train dogs to rape people.
- James Bloodworth shows how "socialism has morphed into a racket" in Cuba.
- The United States has a long history of failing to manage pandemics.
- Chicago Public Schools plans to cut teachers (but apparently not useless administrators) to plug a $732 million deficit. It won't work, because the teachers aren't the problem.
- C# 15 has union types? Kewl.
Finally, after almost two years, the Chicago Dept of Transportation has just about finished rebuilding four bridges around Montrose Harbor. This is relevant to Cassie and me because it means a slightly shorter path from our new place to the Montrose Dog Beach. I haven't paced it out yet, but I believe the dog beach is just under 1,500 meters away. We will find out soon.
I forgot to mention, I broke down and bought a NetGear Nighthawk RS700s yesterday. Whoo boy:
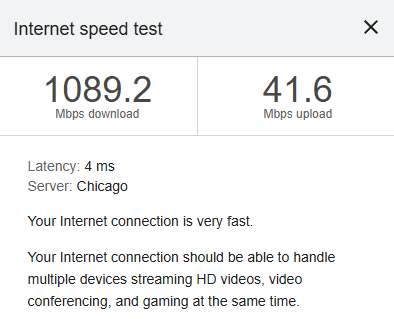
My old router could only manage 250 Mbps on a good day. The difference is noticeable, especially when I watched the latest episode of "The Boys" last night. Whee!
NB: Never mind that upload speed; the building has cable, which will always have slower uploads than downloads.
With all of the move finally completed, including all the unpacking and all the little things you need to do in a vacant house before closing, I'm OK with where I wound up. The apartment is temporary, though that could wind up being a couple of years, during which time I will have to maintain more than one storage locker full of my stuff. I may miss the movie collection the most. (I can always go to the storage facility and grab a movie if I need to. The boxes are pretty well labeled.)
I do like this view, though, especially when the sun is setting behind me:

I might even take myself to a movie this evening. I haven't seen Project Hail Mary yet.
Copyright ©2026 Inner Drive Technology. Privacy. Donate!